BMW Bug Bounty – Account Verification Bypass writeup
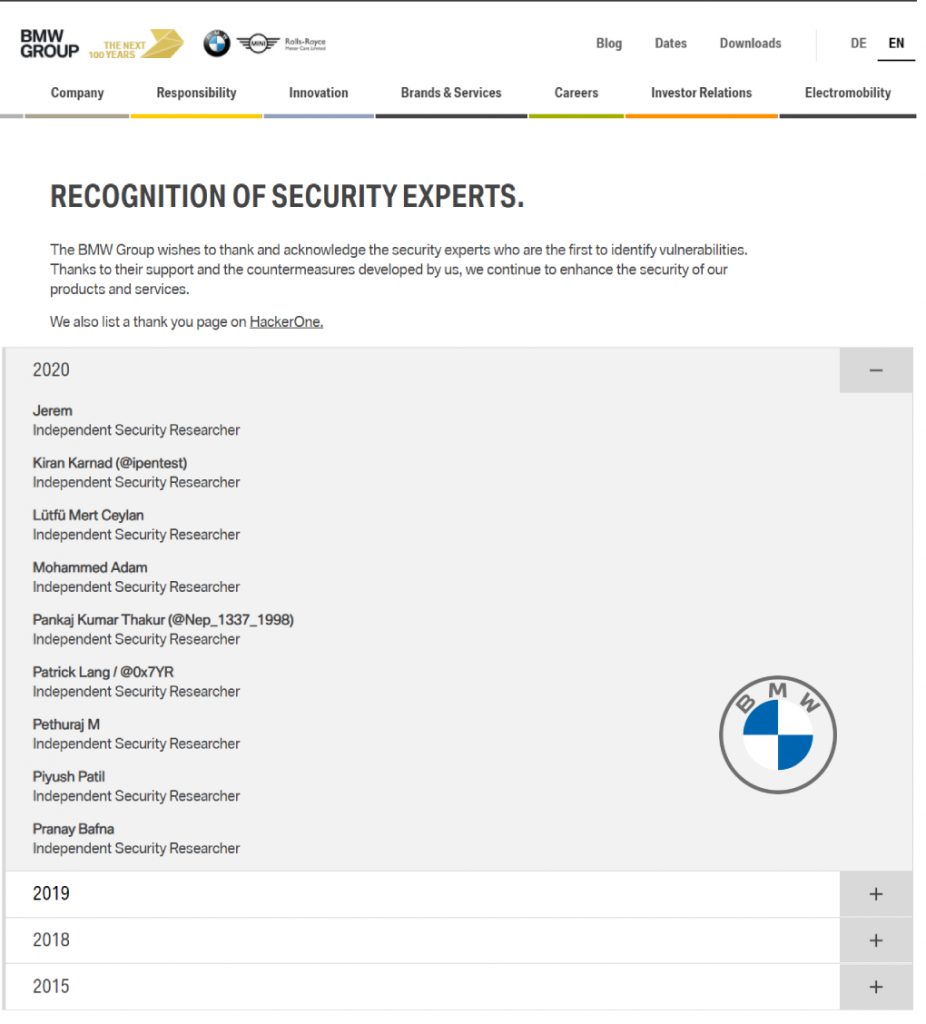
It all started with the BMW Security Experts Acknowledgment page, missing my name and I decided to give it a try.
I started with the BMW security page and tested BMW Singapore website as per their policy and I picked https://accessbybmw.com.sg/ domain as my target and quickly started the recon activity.
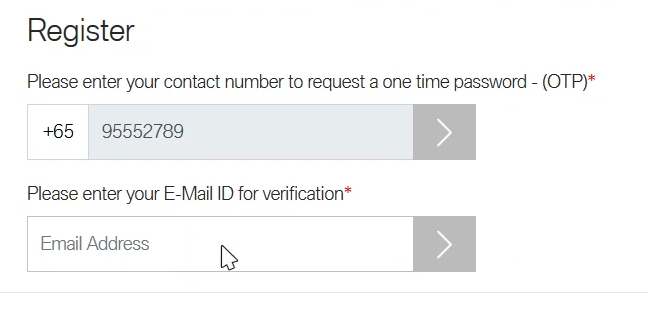
So, this application has a lot of functionalities and an account registration and login page. To register for an account – I need to use a Singapore mobile number.
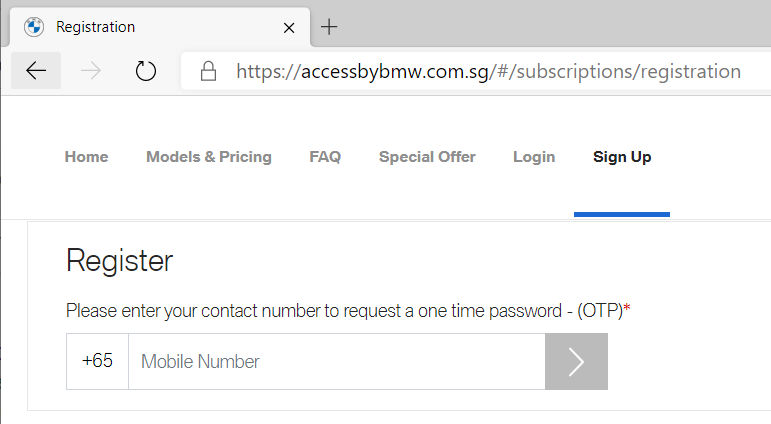
So I picked a disposable mobile number (there are so many sites that offer these services) which lets us receive SMS when creating an account.
I entered the mobile number and started to brute force the OTP and I understood that the OTP is four digits long with just only numerals.
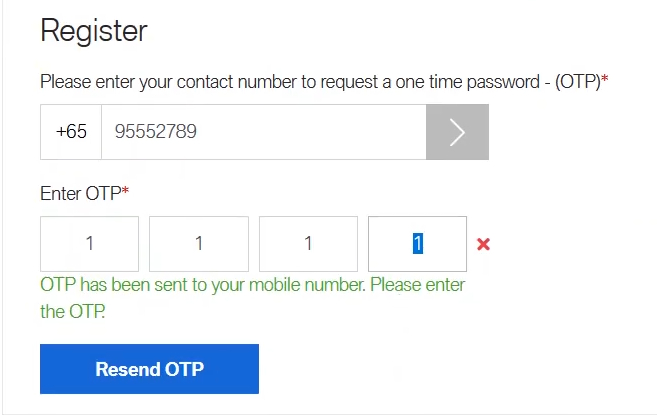
I captured the request in Burp suite and sent to the intruder to brute force the OTP with the payload type as four-digit numbers which ranged from 0000-9999.
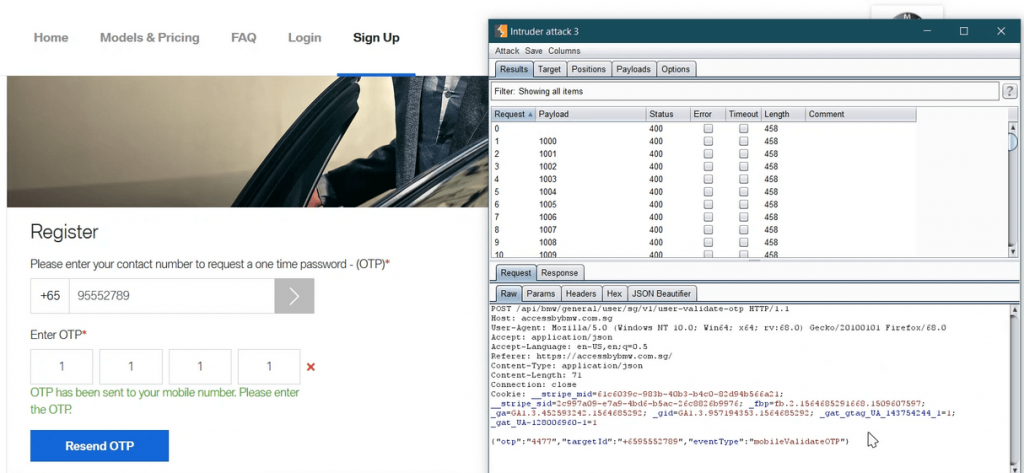
By analysing the Http response from the intruder tab – it was observed that the wrong OTP returns 400 status code.
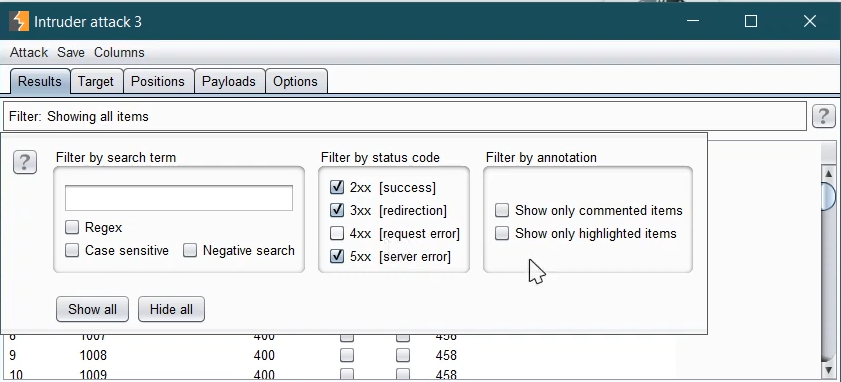
So, I filtered the status code which does not contain 4xx series of status codes.
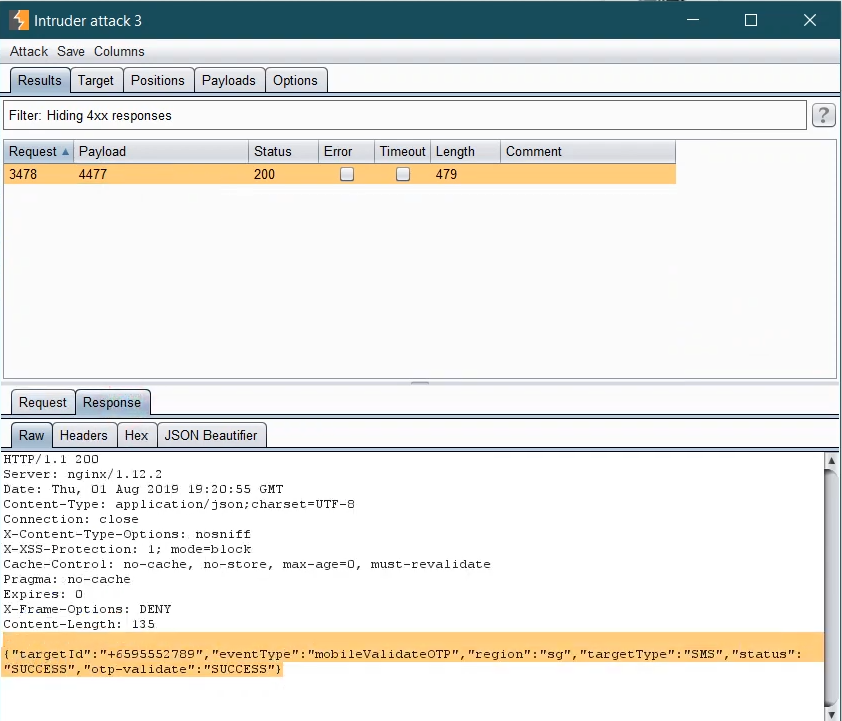
Now I could see a request popping up in the intruder tab returning 200 status code as per the filter.
By analyzing the response – I can see the OTP is accepted.
Upon entering the OTP in the browser – it got accepted.
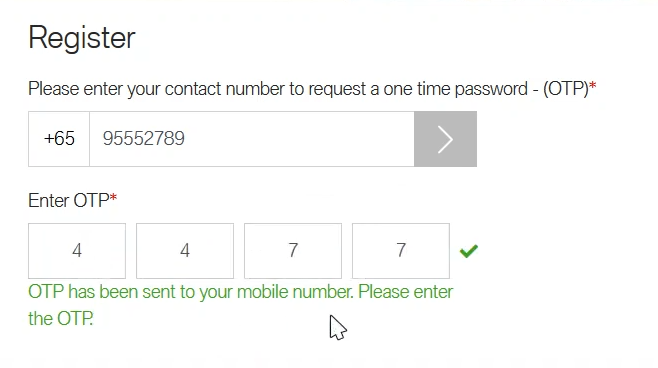
Boom! So here comes the next step to provide with Email address field to continue with the registration process thus bypassing the Account verification.
For reporting this security flaw to BMW – I’m honoured on their Security Experts Acknowledgment page.
You can find the acknowledgement here :
https://www.bmwgroup.com/en/Security.html
You may like!
How to use Burp Suite Like a PRO? PART – 2